Wazuh - Open Source SIEM
Wazuh is a free and open source security platform that provides unified SIEM and XDR protection. It protects workloads across on-premises, virtualized, containerized, and cloud-based environments.
The Wazuh platform uses a server/agent model:
- Wazuh central components (server, indexer, and dashboard) that analyze security data collected from the agents. They can be set up on-premises or in the cloud using the Wazuh Cloud solution.
- Lightweight and universal security agents are deployed on monitored endpoints to collect security data and perform automatic responses to threats.
The Wazuh solution also provides agentless monitoring for devices such as routers, firewalls, and switches that do not support the installation of agents.
Overview
Businesses need to be confident that their infrastructure is secure against digital threats. Poor data security can lead to data breaches and security incidents that negatively impact a business and its customers.
If cyberattacks are not promptly detected and mitigated, the aftermath can be expensive, time-consuming, and result in the loss of sensitive information.
Over time, cybercriminals have improved their techniques for evading basic security solutions. Therefore, businesses require a strong security plan.
The use of extended detection and response platforms (XDR) can improve an organization’s security posture.
An XDR is a platform that provides visibility, detection capabilities, and effective response to threats in an enterprise environment.
Introducing Wazuh
Wazuh is a free and open source security platform that provides unified SIEM and XDR protection. It protects workloads across on-premises, virtualized, containerized, and cloud-based environments.
The Wazuh platform uses a server/agent model:
- Wazuh central components (server, indexer, and dashboard) that analyze security data collected from the agents. They can be set up on-premises or in the cloud using the Wazuh Cloud solution.
- Lightweight and universal security agents are deployed on monitored endpoints to collect security data and perform automatic responses to threats.
The Wazuh solution also provides agentless monitoring for devices such as routers, firewalls, and switches that do not support the installation of agents.
In the following sections, we see some Wazuh capabilities that make it a comprehensive XDR.
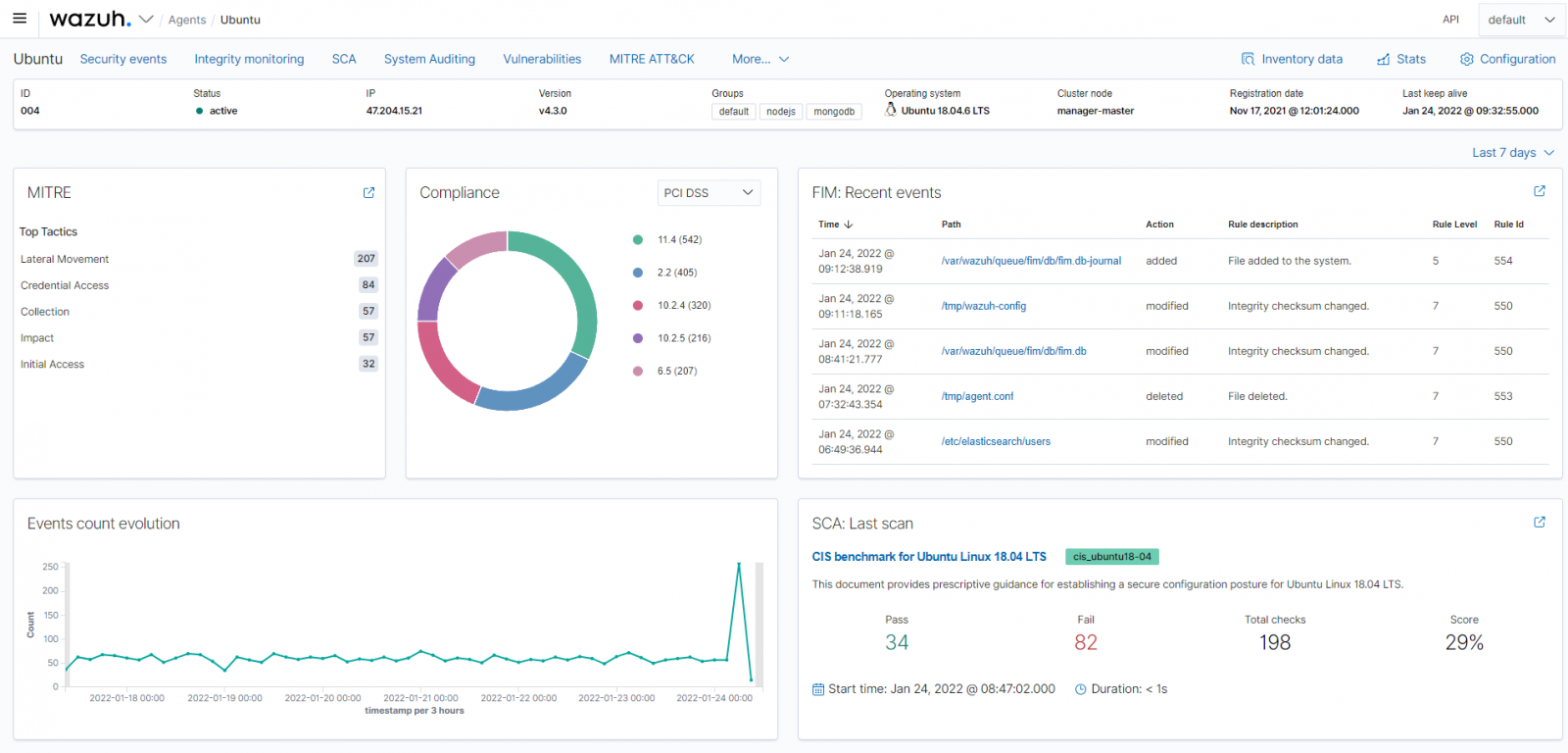
Endpoint security
Wazuh provides capabilities for threat prevention, detection, and response. The Wazuh agents installed on endpoints do the following:
- Collect security data.
- Report misconfigurations and security issues.
- Monitor file system and report changes.
In addition to security visibility and monitoring of endpoints, Wazuh provides self-defense capabilities and automated responses to detected threats. The Wazuh solution can perform responsive actions like removing malicious files, blocking malicious network connections, and other countermeasures.
Security Operations
An important feature of an XDR is its ability to aggregate, normalize, and correlate data from multiple sources. Wazuh collects large volumes of events across various devices and analyzes them to generate valuable security information.
The security agents have an anomaly and malware detection module which detects abnormal and malicious events on endpoints.
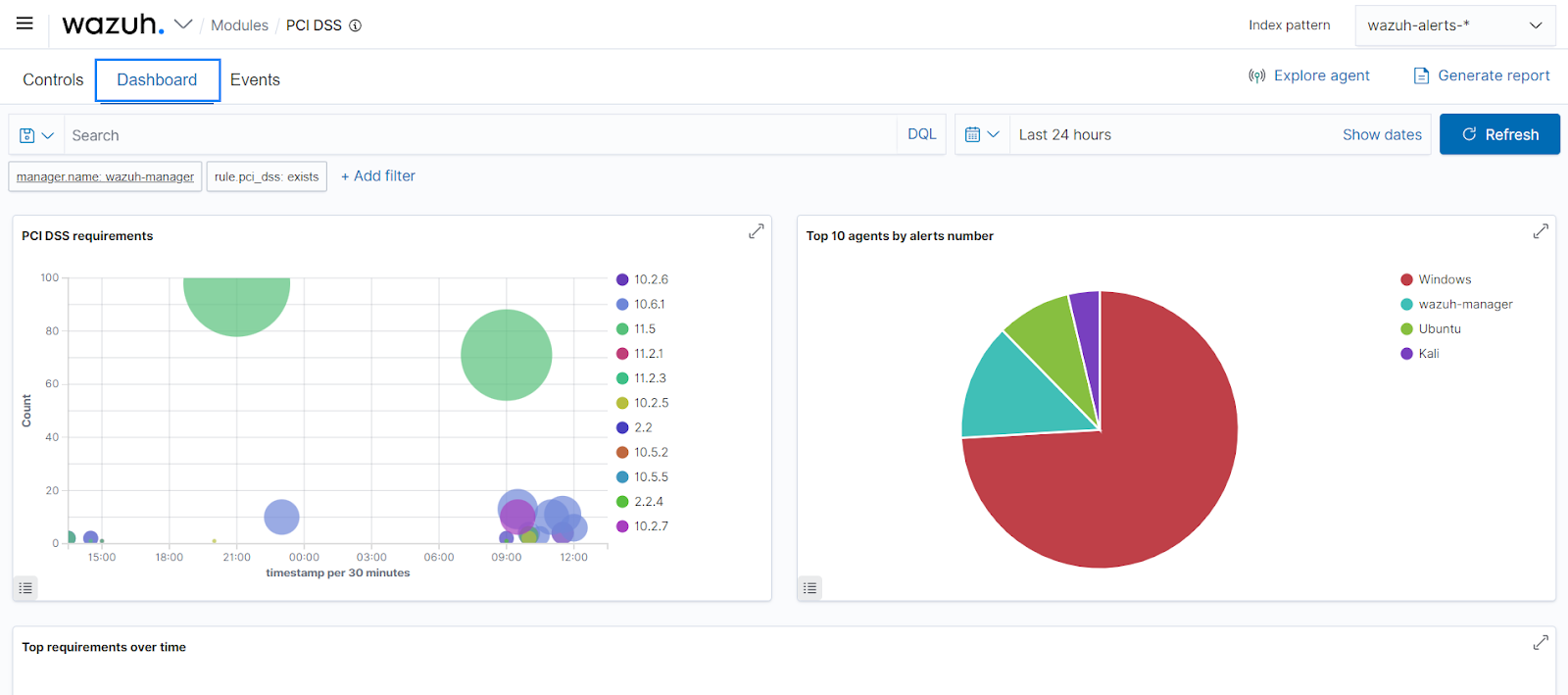
Wazuh supports regulatory compliance by using rulesets that are carefully mapped against compliance requirements. Wazuh provides out-of-the-box support for compliance frameworks like PCI DSS, HIPAA, GDPR, NIST SP 800-53, and TSC.
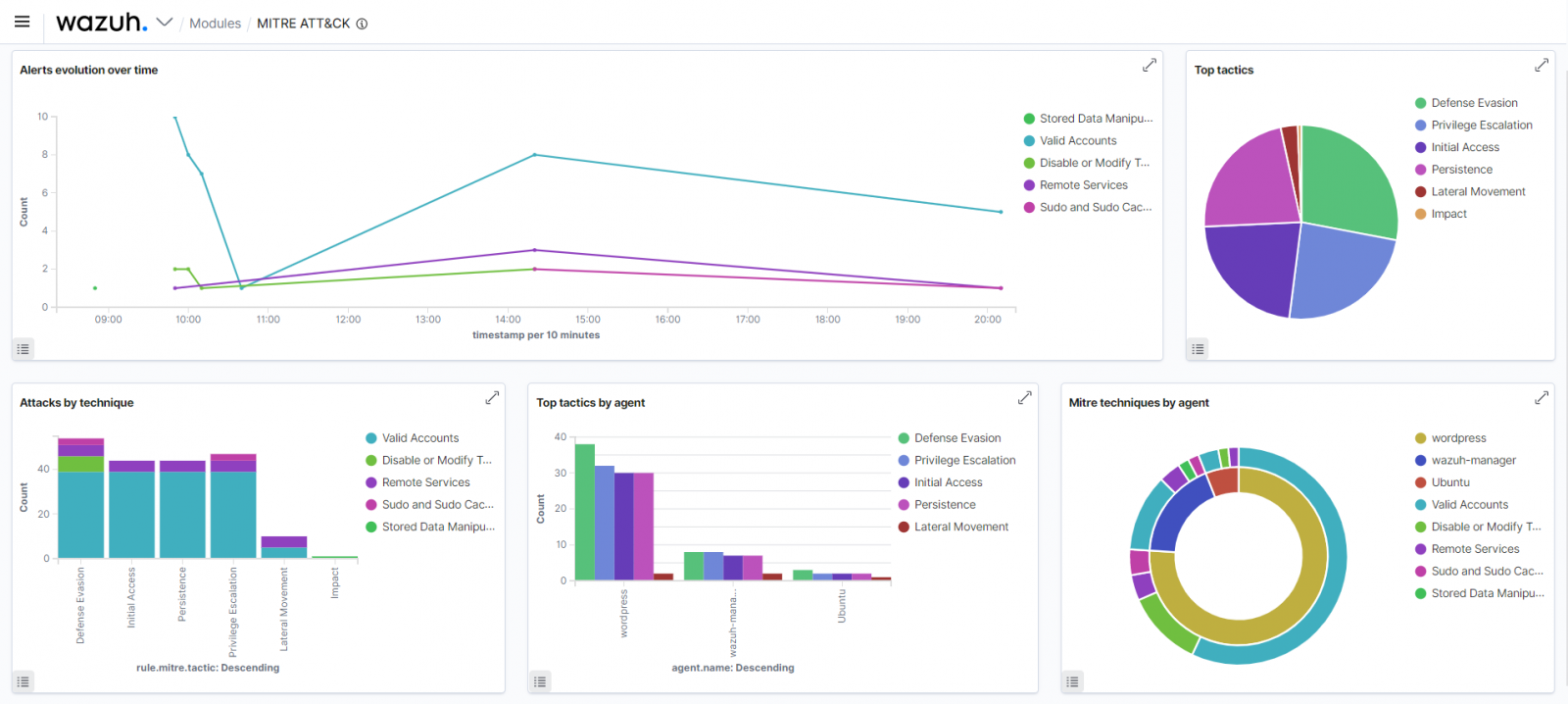
Threat Intelligence
Cybersecurity researchers and threat actors continue to find and exploit vulnerabilities in computer systems. It is, therefore, important for businesses to be aware of old and new vulnerabilities present in their IT infrastructure.
Wazuh has an inbuilt vulnerability detection module that periodically scans installed applications to find vulnerabilities. It correlates data received from the endpoints with up-to-date CVE (Common Vulnerabilities and Exposure) databases and provides security visibility.
The Wazuh solution also incorporates the MITRE ATT&CK framework to quickly recognize and hunt for adversary tactics, techniques, and procedures (TTPs) across an enterprise environment. Event alerts are mapped to their associated MITRE ATT&CK technique to include useful information.
Cloud Security
Businesses are increasingly relying on cloud-native solutions to host their services. Wazuh, in this regard, not only provides real-time protection for on-premises workloads but also for cloud infrastructure.
It can be integrated with cloud services like Google Cloud Platform (GCP), Amazon Web Services (AWS), and Microsoft Azure to provide cloud-level security to these infrastructures. Taking a step further, the Wazuh solution puts containerized workloads in mind by providing protection for popular technologies like Docker and Kubernetes.
Free and Open Source
Wazuh is one of the fastest growing open source security solutions, with over 10 million downloads per year. Wazuh provides communities where users can engage Wazuh developers, share experiences, and ask questions related to the platform.
Being free and open source provides an opportunity for scalability and customization. This platform can be easily integrated with other open source tools and security solutions to enhance its XDR capabilities. Some of its integrations include VirusTotal, Suricata, YARA, and Slack, to name a few. Check out this documentation on how to get started with Wazuh.
Sponsored and written by Wazuh.
Compliance Achievable with Wazuh & Relevant Requirements
Wazuh is an open-source security platform that provides SIEM (Security Information and Event Management), XDR (Extended Detection and Response), log monitoring, intrusion detection (IDS), file integrity monitoring (FIM), and compliance auditing. Below are key compliance frameworks that Wazuh supports, along with specific requirements and how Wazuh helps meet them.
1. ISO 27001 (Information Security Management System - ISMS)
Relevant Requirements & How Wazuh Helps
| ISO 27001 Clause | Requirement | How Wazuh Helps |
|---|---|---|
| A.12.4.1 | Event logging | Collects and analyzes system logs for security monitoring. |
| A.12.4.2 | Protection of log information | Encrypts and secures logs to prevent tampering. |
| A.12.6.1 | Vulnerability management | Detects vulnerabilities in applications and systems. |
| A.16.1.1 | Incident response process | Provides alerts and forensic analysis for security incidents. |
✅ Why?
Wazuh enhances ISO 27001 compliance by offering log management, security monitoring, and vulnerability detection.
2. PCI DSS (Payment Card Industry Data Security Standard)
Relevant Requirements & How Wazuh Helps
| PCI DSS Requirement | Requirement | How Wazuh Helps |
|---|---|---|
| Req. 10.2 | Logging and monitoring of user activities | Monitors file changes, system events, and login attempts. |
| Req. 10.6 | Regular log review | Provides automated log analysis and anomaly detection. |
| Req. 11.5 | File integrity monitoring (FIM) | Detects unauthorized modifications to sensitive files. |
| Req. 12.10 | Incident response | Generates real-time alerts for security events. |
✅ Why?
Wazuh helps organizations meet PCI DSS compliance by providing log monitoring, intrusion detection, and file integrity monitoring.
3. GDPR (General Data Protection Regulation)
Relevant Requirements & How Wazuh Helps
| GDPR Article | Requirement | How Wazuh Helps |
|---|---|---|
| Art. 25 | Privacy by design | Provides security monitoring to prevent data breaches. |
| Art. 32 | Security of processing | Ensures continuous system monitoring and intrusion detection. |
| Art. 33 | Breach notification | Detects and alerts on data breaches in real time. |
| Art. 35 | Data Protection Impact Assessment (DPIA) | Assists in risk assessment by identifying security vulnerabilities. |
✅ Why?
Wazuh enhances GDPR compliance by offering real-time breach detection, log management, and risk analysis.
4. HIPAA (Health Insurance Portability and Accountability Act)
Relevant Requirements & How Wazuh Helps
| HIPAA Security Rule | Requirement | How Wazuh Helps |
|---|---|---|
| 164.308(a)(1)(ii)(D) | Regular security monitoring | Monitors system logs and access records. |
| 164.312(b) | Audit controls | Collects security logs for compliance auditing. |
| 164.312(c)(1) | Data integrity protection | Detects unauthorized changes to critical files. |
✅ Why?
Wazuh helps healthcare organizations protect patient data by ensuring log monitoring, access control, and intrusion detection.
5. NIST 800-53 (National Institute of Standards and Technology - Security Controls)
Relevant Requirements & How Wazuh Helps
| NIST Control ID | Requirement | How Wazuh Helps |
|---|---|---|
| AU-6 | Audit log review | Stores, reviews, and analyzes security logs. |
| SI-4 | System monitoring | Detects security threats using SIEM and IDS. |
| CA-7 | Continuous security monitoring | Provides real-time alerts for security events. |
✅ Why?
Wazuh supports NIST 800-53 compliance by ensuring security event monitoring and automated log analysis.
6. SOC 2 (Service Organization Control 2 - Security & Availability)
Relevant Requirements & How Wazuh Helps
| SOC 2 Trust Principle | Requirement | How Wazuh Helps |
|---|---|---|
| Security | Protection from unauthorized access | Detects and prevents security threats. |
| Availability | Ensures system uptime and reliability | Monitors system health and logs security events. |
| Processing Integrity | Ensures IT operations function correctly | Provides alerts for unauthorized file changes. |
✅ Why?
Wazuh enhances SOC 2 compliance by offering security monitoring, log integrity, and incident detection.
7. ISO 22301 (Business Continuity Management - BCMS)
Relevant Requirements & How Wazuh Helps
| ISO 22301 Clause | Requirement | How Wazuh Helps |
|---|---|---|
| 8.4.3 | Incident monitoring & response | Detects and alerts on security threats. |
| 8.5.1 | Business continuity monitoring | Ensures uptime of critical IT infrastructure. |
| 9.1.1 | Performance monitoring | Tracks system performance and anomaly detection. |
✅ Why?
Wazuh helps business continuity planning by monitoring security events and system performance.
8. CIS Controls (Center for Internet Security)
Relevant Requirements & How Wazuh Helps
| CIS Control | Requirement | How Wazuh Helps |
|---|---|---|
| CIS Control 3 | Continuous vulnerability management | Scans for security vulnerabilities and misconfigurations. |
| CIS Control 6 | Audit log management | Provides centralized log collection and analysis. |
| CIS Control 8 | Malware defenses | Detects and alerts on security anomalies. |
✅ Why?
Wazuh helps organizations follow CIS security best practices by detecting threats and maintaining audit logs.
9. ITIL (Information Technology Infrastructure Library)
Relevant Requirements & How Wazuh Helps
| ITIL Process | Requirement | How Wazuh Helps |
|---|---|---|
| Incident Management | Detect and resolve IT incidents | Monitors system logs and alerts on security issues. |
| Problem Management | Identify recurring IT issues | Provides insights into security threats and vulnerabilities. |
| Change Management | Monitor IT infrastructure changes | Tracks system modifications and unauthorized access. |
✅ Why?
Wazuh aligns with ITIL best practices by providing IT security monitoring and incident response.